|
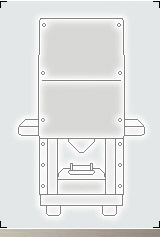
HDC FEATURES
Transportable;
EU 230VAC 50/60 cycle (0.37kW);
10 second cycle time;
Crush over 60 disks an hour;
Visual verification of destruction;
Safety switch on destruction chamber;
Durable and transportable;
Simple, safe and secure
|
 |
 |
ENDORSEMENT:
"Current practice in the area of computer forensics relies on the ability of a computer hard-drive to function correctly with regard to the reading and writing of data to the device via an ATA data/command channel. If a computer hard-drive is physically damaged, then data recovery techniques focus on the creation of a working drive via platter swapping, head swapping and hot swapping of controller boards. If the disk platter is physically damaged or deformed then current computer forensics, and data recovery techniques are ineffectual in facilitating the extraction of data from the hard drive. When a disk platter is physically deformed and/or physically damaged there is currently no technology that will easily allow for the complete or partial recovery of data from the device."
Prof. Andrew Blythe
University of Glamorgan
Reclamere has been the owner of the HDC for several years. We have been extremely pleased with the through-put of the device and the very responsive customer service. As a forensic services and data recovery company, we are on the cutting edge of recovering data from damaged hard drives. We have complete confidence that drives processed through the HDC are unrecoverable by any means available to commercial data recovery experts, and may very well be totally unrecoverable. Our financial services, government and healthcare clients have been thrilled with our onsite services provided with the HDC. Reclamere has complete confidence in the HDC process and eDR Solutions for our physical hard drive destruction needs.
Angie Singer Keating
VP Compliance and Security Reclamere
|
 |
|
|
The Problem
Every day the issue of identity and data theft is becoming more common. £1.7 billion is estimated to be the loss suffered in the UK by companies and individuals by the misuse of confidential and personal data.
Companies affected by misuse of data report loss of customer confidence and trust after the incident as a negative factor in their ongoing ability to attract and retain business. BBC News recently highlighted a Which Computing report that 22,000 "deleted" files were recovered from eight computers purchased on eBay. Criminals obtain computers from internet sites, second hand sales and rubbish tips. Large scale "factories" are in operation where recovered hard disk drives are scanned for useful information which is then sold on to unscrupulous users.
The Information At Risk
All modern organisations now use computers in every aspect of daily operations. No matter what type of organisation, those computers will contain sensitive data. That could be strategic business plans, customer lists, confidential contracts, pricing information, firewall configuration files, encryption keys, the list is endless. For companies dealing directly with the public such as retailers or banks, thousands and thousands of credit card or bank account details, addresses and phone numbers. All highly protected under the obligations of the Data Protection Act.
It is much simpler and faster to use the Hard Disk Crusher than it is to reformat a disk or use a degausser. Furthermore, it has been proven that degaussers don't always work. New disks have such strong shielding that the magnetic oersteds (Oe) used to destroy the data can only achieve a high enough field intensity to destroy the read-write arm. Therefore it's often possible to remove the platters, put them in a new disk housing with a new read-write arm, and read the data that you thought you had destroyed. Unfortunately, due to new disk shielding technologies, degaussers have become unreliable.
What Happens?
Computing or data storage equipment is regularly renewed as the requirement for more speed or storage evolves. In the past many companies have paid little or no thought to the end destination of old, broken or obsolete models. Even when a desirable solution such as charitable donation has been chosen, the final destination of the equipment and the information contained on it has often proved to be highly undesirable. Think about it, every email you have ever sent, every password to every system you use, every website ever visited, every document you have ever created are all easily available in todays sophisticated world of cyber thieves.
What About Reformatting?
Reformatting relies on knowing the type of drive beforehand, (SCSI, SCSI2, SATA etc.) often involving an expensive site survey, as well as the fact the drive itself must be in a working condition for the reformatting software to work. Setting up the right interface and then running the programme up to six times is very time consuming and again there is no obvious verification that the data has been destroyed. Though reformatting a disk can wipe out the date, it is very time consuming. It can take hours to reformat one disk. And the system reformatting the disk needs to be operational. The Hard Disk Crusher can destroy a disk and the data on it in just seconds without the need of a peripheral PC or workstation.
What About Degaussing?
Methods such as degaussing, reformatting and overwriting are in use but can be costly, time consuming and may not work on many modern drives with high shielding. All degaussers have a limit to which they will be successful. The majority can only remove data up to 1700 oersted shielding, whilst many hard drives are now protected to up to 4000 oersted. Degaussing uses a great deal of electrical energy and produces a lot of heat. The machines require a cool down period of at least 20-30 minutes between cycles. There is no obvious verification that the data has been destroyed as the drive looks identical from start to finish.
What The Experts Say
Experts recommend the only way to ensure data destruction is to physically destroy the hard disk drive as reported by Which Computing, IT Pro and the Daily Mail and many other publications. Physical destruction of modern drives has in the past been difficult as it has only been available by transporting the entire computer to a site with industrial shredding capability. Industrial shredding machines must use wheels of the correct size to actually destroy the drives. In mixed waste shredders the wheels are often too large to destroy 3.5 or 2.5 drives immediately. Your data is insecure as soon as the equipment leaves your premises and may not reach its destination!
It is rare for organizations and companies not to have sensitive information on their hard disks. The Hard Disk Crusher can help you ensure that the following types of information remains private:
- Bank account numbers
- Biometric information
- Classified information
- Copyrighted material
- Corporate financial records
- Credit card numbers
- Department of Defense secrets
- DNA records
- Driver's license numbers
- Encryption keys
- Firewall configuration files
- Information security documents
- Investment account information
- Medical records
- Law enforcement records
- Legal cases and records
- Login and password information
- National security information
|
- Passport numbers
- Patents
- Personal email
- Pharmaceutical formulas
- Political campaign secrets
- Pornography
- Proprietary information
- Retirement account information
- Router ACLs
- Security configuration files
- Sensitive customer information
- Social Security numbers
- Standardized test scores
- Stock trades
- Strategic business plans
- Tax records
- Trade secrets
|
|
|
|